Last year, we launched Formulas and Actions, powerful tools for automating more of your fraud review workflow. Since then, we’ve gotten a lot of positive feedback from customers about how Actions are helping them streamline fraud management, but we’ve also gotten some questions about best practices. In this blog post, we’ll share guidelines for the best, most secure way to use Actions Webhooks to automate tasks that need to be done asynchronously.
As a very first step, you’ll need to set up some Actions, and create Formulas which will trigger those actions. You can read all about how to do that in our Formulas and Actions Tutorial.
Already got Actions set up? Great! The next step is to set up Actions Webhook Signing to validate that notifications are coming from us. Here’s how to get Actions Webhook Signing running in 3 easy steps:
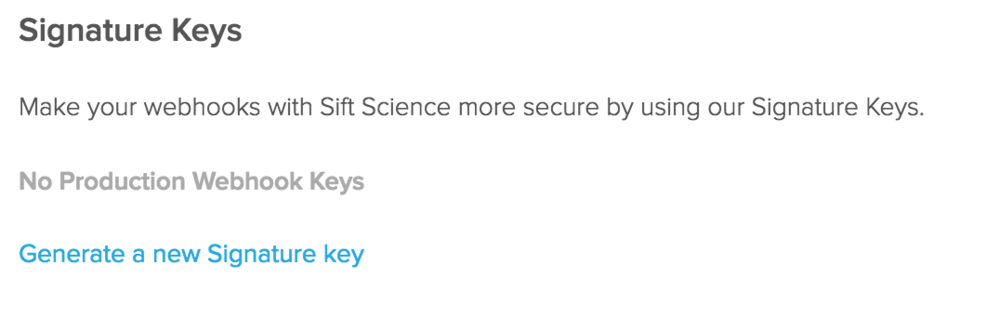
Step 1: Before setting up Action Webhooks, you’ll want to enable webhook signing so that you can verify that the notifications are coming from Sift Science. To do so, go to the API Key Tab of our developer page in the Sift Science console. There you’ll see a section called Signature Keys:
Step 2: Click on “Generate a new Signature key”, and activate the signature key:
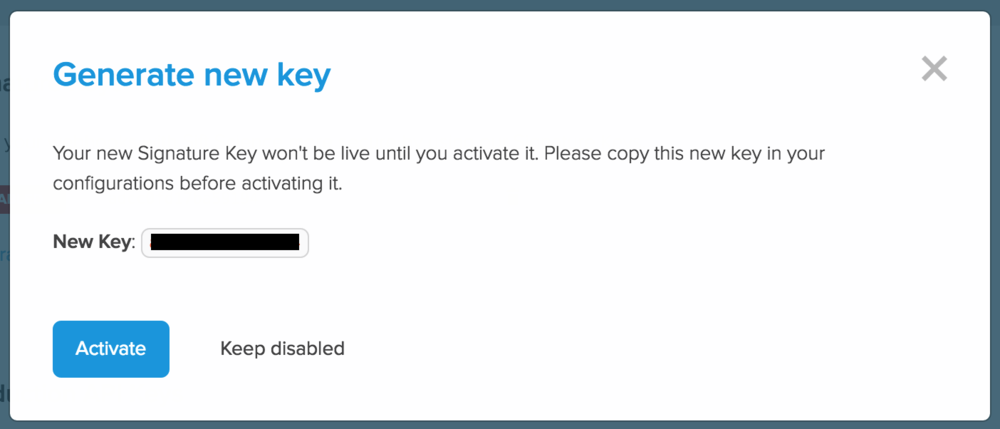
Your new signature key is active! You may only have one active key at a time. Make a note of it, because you’ll use it later in your code base.
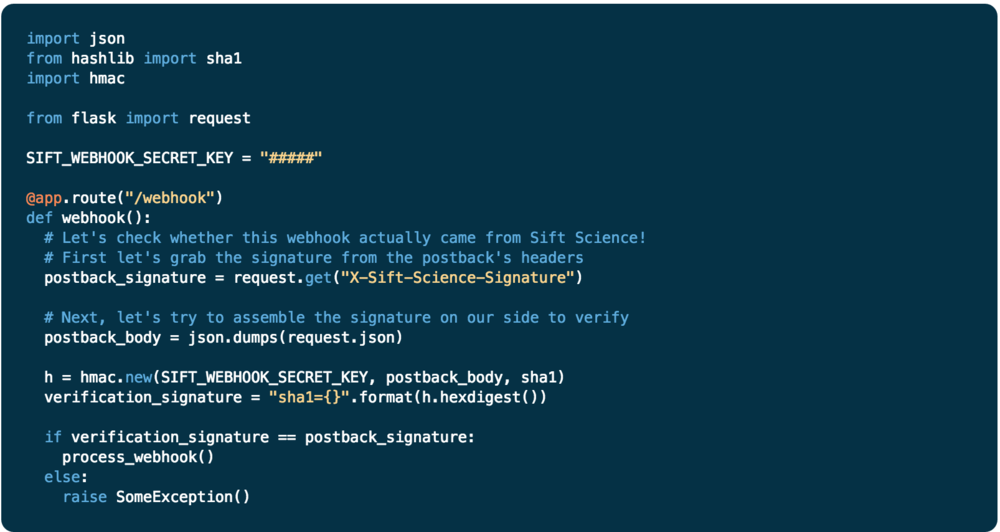
Now that you’ve enabled webhook signing on Sift Science, all webhook notifications generated by our Formulas and Actions will have a signature in the HTTP header under “X-Sift-Science-Signature”. This signature is calculated by generating an SHA-1 hash of your signature key and the body of the notification.
Step 3: In order to verify than an http notification is coming from Sift Science, create an SHA1 hash of your signature key combined with the body of the notification you received and compare it to the signature value in the HTTP header. It’s that easy! Here’s some sample code to give you an idea of how your webhook verification should operate:
For additional code examples, check out our webhook authentication documentation. Questions? Contact us anytime at [email protected]. Thanks for tuning in!